Understanding the CrowdStrike Phishing Campaign: A Deep Dive into a Growing Threat
Cybersecurity threats are constantly evolving, and one of the most recent warnings comes from CrowdStrike, a leading cybersecurity firm. On January 7, 2025, the company alerted the public about a sophisticated phishing campaign targeting job seekers by impersonating CrowdStrike itself. This article explores the intricate details of this phishing attempt, the tactics used by the attackers, and how individuals can safeguard themselves against such deceptive practices.
The Attack Framework: A Crafty Approach
At the heart of this malicious operation is a well-crafted email masquerading as a communication from a CrowdStrike recruitment agent. The email thanks job seekers for applying for a developer position, ingeniously luring them into a false sense of security. This initial approach aims to create credibility, which is a hallmark of successful phishing scams.
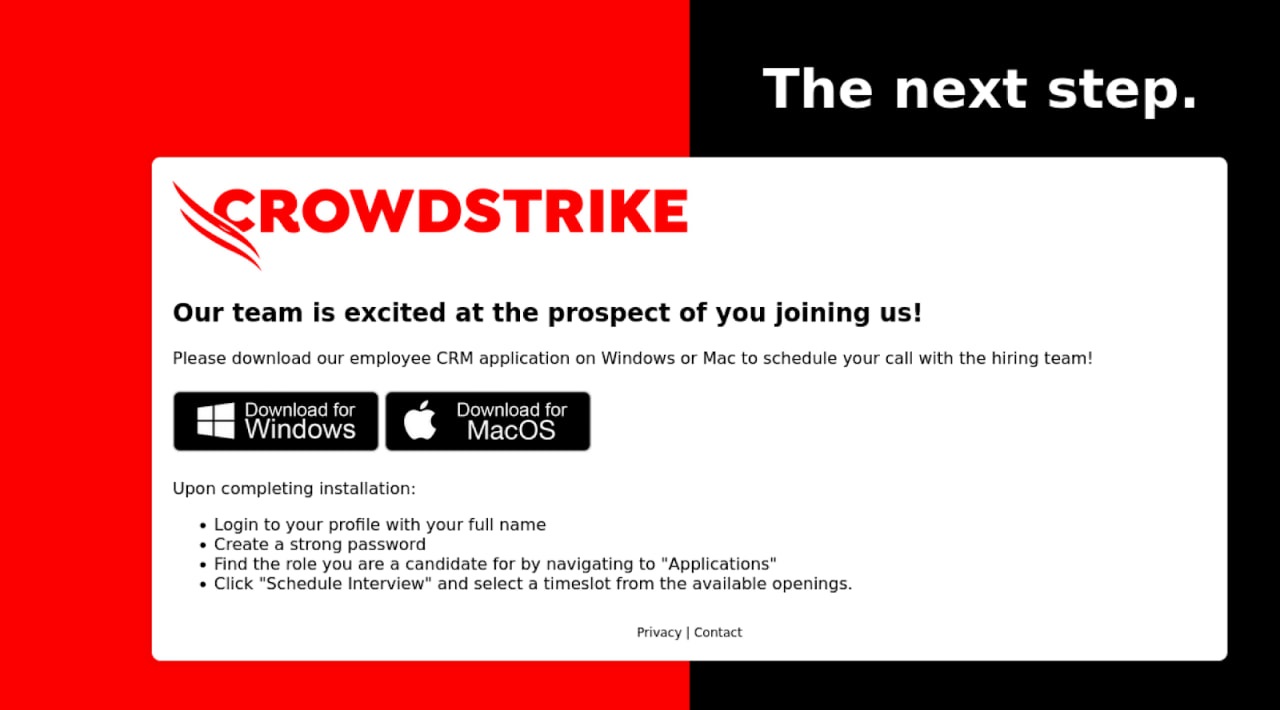
Upon clicking the embedded link in the email, unsuspecting candidates are redirected to a fraudulent website designed to mimic an official CrowdStrike portal. Here, they are invited to download a so-called "employee CRM application," which the attackers falsely claim is part of a new onboarding process. This level of detail demonstrates the attackers’ commitment to designing a convincing narrative that would easily deceive even the most cautious individuals.
The Malicious Website: An Expert Duplication
The phishing email directs victims to a website with the URL "cscrm-hiring[.]com." The design of this page mirrors CrowdStrike’s legitimate portal, enhancing the likelihood that victims will unwittingly trust and engage with it. This malicious site offers downloads for both Windows and macOS, catering to a broader range of potential victims.
The sophistication of this operation extends to the way the downloaded tool operates. Before executing its malicious payload, the tool performs checks to identify whether it runs in a sandbox or analysis environment. This tactic is crucial for the attackers, as it allows them to ensure that their malware runs only on actual victims’ machines, thereby maximizing the success of their operation.
Infiltration Techniques: The Malware Unleashed
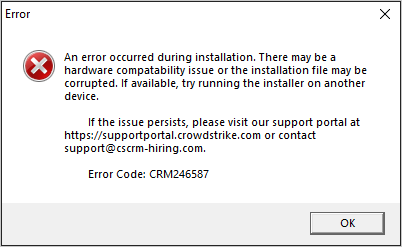
Once a candidate downloads the supposed CRM application, they are met with a deceptive error message stating that the installer file might be corrupt. This false message serves two purposes: it diverts the victim’s suspicion and allows the malware to proceed undetected in the background.
While the victim perceives the error, the tool quietly retrieves a configuration file necessary for running XMRig, a Monero cryptocurrency miner. The actual miner is then downloaded from a GitHub repository and unpacked into a seemingly innocuous location on the victim’s computer, specifically the ‘%TEMP%\System\’ directory. This method allows the malware to blend in with other legitimate processes on the victim’s system.
Persistence and Avoidance of Detection
To maintain its presence on the compromised machine, the miner employs several tactics. It is programmed to run in the background, utilizing minimal processing power (up to 10%) to avoid detection by the victim. Additionally, a batch script is placed in the Start Menu’s Startup directory, thus ensuring the malware continues to run each time the victim boots their computer.
Further complicating detection efforts, a logon autostart key is added to the Windows registry. Such extensive measures demonstrate the attackers’ commitment to maintaining access over a prolonged period, maximizing the profit gained from the compromised machine.
Safeguarding Against Phishing Attacks
With the rise of sophisticated phishing campaigns like this one, caution is paramount, especially for job seekers eager to land their next opportunity. CrowdStrike emphasizes the importance of verifying the legitimacy of communication. Job candidates should always scrutinize the sender’s email address, ensuring it aligns with the official company domain. If in doubt, reaching out via established channels found on the company’s official website is crucial.
Moreover, candidates should be wary of any messages demanding urgent responses or offering deals that seem too good to be true. It is essential to remember that legitimate employers rarely require candidates to download third-party applications as part of the recruitment process, nor do they request upfront payments.
Ultimately, awareness and vigilance are the first lines of defense against these increasingly sophisticated phishing schemes. Cybersecurity is a collective responsibility, and understanding the tactics employed by attackers plays a vital role in protecting oneself from malicious threats.
Further information about this particular campaign, including indicators of compromise, can be found in CrowdStrike’s detailed report here.